Inside the Platform
A visual walkthrough of the ShadowMask workflow.
Login / Signup
It provides password reset, remember‑me, and account‑lockout protections, plus clear error and recovery flows. Role-based access control enforces capabilities: regular users can upload and process documents, view and rehydrate their own masked data, and manage personal settings. Admins can manage users and roles, review audit logs, configure global PII rules and encryption/key settings, and access organization‑level reports.
Chat
The chat feature allows users to securely interact with the AI assistant directly within the app interface. Users can ask questions, request document processing, or get explanations about masked data and rehydration steps. The chat supports context-aware follow-up, so users can reference previous messages or documents during a session. All chat data is processed locally or securely, ensuring sensitive information is not sent to third-party servers. Admins can review chat logs for compliance and troubleshooting, if enabled by organization policy.
Admin Dashboard
Centralized Admin UI: Dedicated dashboards for Users, PII Rules, Encryption Keys, and Audit Logs. RBAC Authorization: Secure middleware enforcing strict Admin vs. User access and route protection. Dynamic PII Config: Live NER/Regex toggles with instant previews for document scrubbing rules. Hardware-Level Security: Integrated handlers for OS Keychain/TPM, key rotation, and passphrases. Immutable Audit Logs: Searchable, tamper-evident logging for all masking and document actions. Enterprise Security Stack: Built-in SSO/2FA, session policies, and automated health-check scheduling.
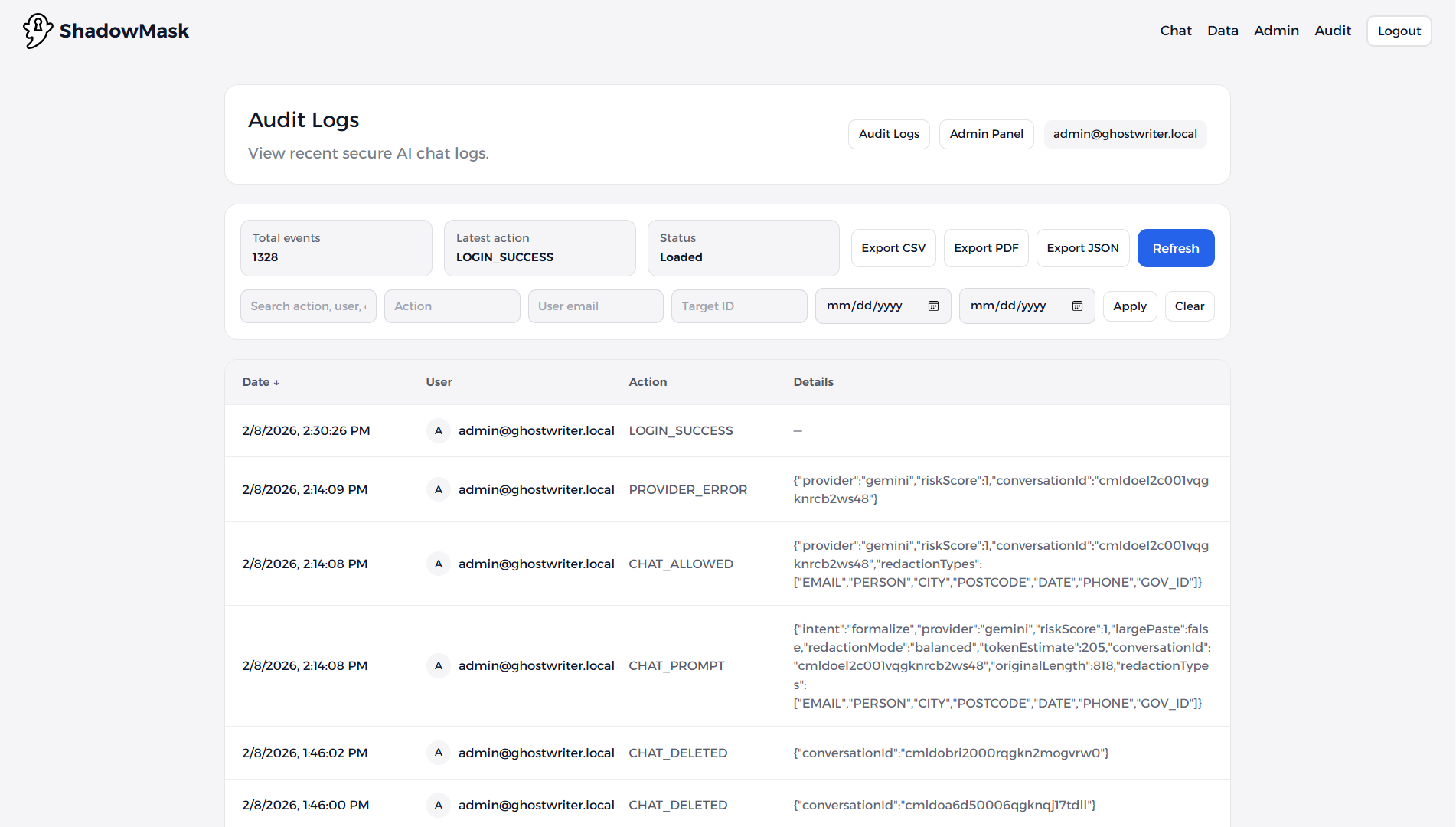
Audit Logs
The audit logs record all key actions in the app, including logins, document uploads, masking, rehydration, user management, and admin changes. Each log entry includes a timestamp, user identity, action type, and relevant details for traceability. Logs are stored securely and can be searched or filtered by admins for compliance, troubleshooting, or security reviews. Audit logs can be exported for reporting or integration with external compliance systems. Tamper-evident mechanisms help ensure the integrity of the logs.
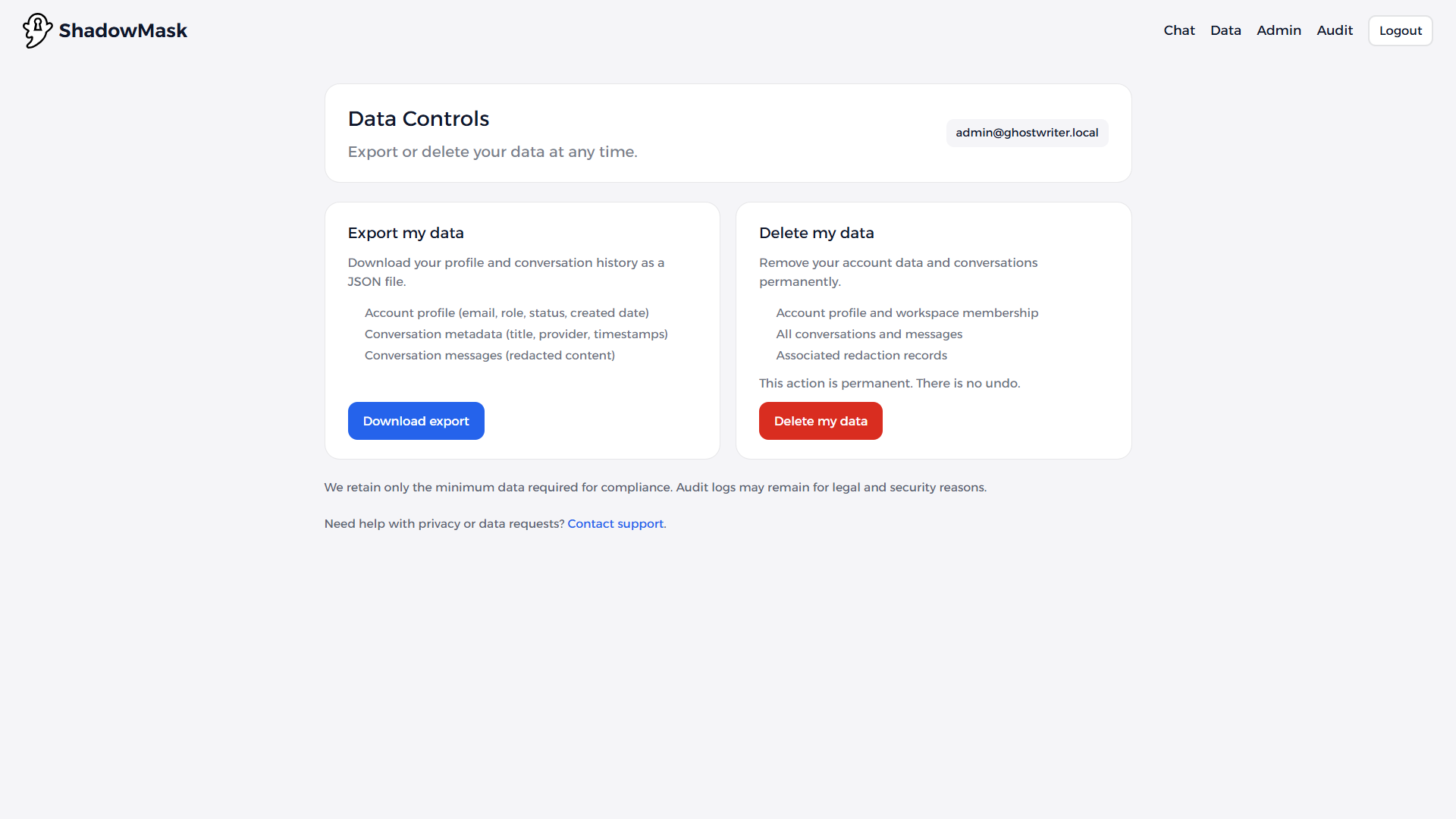
Data Controls
The Data Controls page allows users and admins to manage the lifecycle of uploaded and processed documents. Users can view, download, or delete their own documents and see the status of masking or rehydration. Admins have additional controls to quarantine, permanently purge, or approve/reject rehydration requests for sensitive documents.